SQL, or Structured Query Language, serves as a vital tool for accessing and managing databases. It facilitates tasks like searching, updating, and retrieving data, making it a cornerstone of web application development since its standardization by ANSI in 1986 and ISO in 1987.
SQL Injection (SQLi) poses a significant threat to web security by enabling attackers to infiltrate input fields with malicious SQL statements. This breach grants them control over a database, allowing unauthorized access, data extraction, or manipulation.
Impact of SQL Injection Attacks

The repercussions of a successful SQL injection attack are dire:
- Stolen credentials: Attackers can pilfer user credentials, assuming their identities and privileges.
- Unauthorized database access: Sensitive data stored in database servers becomes vulnerable.
- Data tampering: Attackers can modify or add data to the accessed database.
- Data deletion: Entire database records or tables can be remove.
- Lateral movement: Exploiting operating system privileges, attackers can access other sensitive systems.
Mechanism of SQL Injection Attacks

SQL Injection operates through several stages:
- Identification of vulnerable inputs: Attackers pinpoint inputs susceptible to SQL injection, such as text fields or URL parameters.
- Crafting malicious SQL query: A tailored SQL statement is design to manipulate the application’s original query.
- Bypassing security measures: Techniques like string concatenation or SQL syntax manipulation are employed to circumvent input validation.
- Executing malicious query: The altered query, containing the attacker’s input, is executed by the application.
- Extracting or manipulating data: Depending on the attack, sensitive information may be extracted or data altered within the database.
- Exploiting database server vulnerabilities: Advanced attacks may exploit server vulnerabilities beyond the database.
Types of SQL Injection Attacks

- Union-based SQL Injection: Utilizes the UNION statement to combine select statements, retrieving data.
- Error-based SQL Injection: Causes the application to display database error messages, providing insight into its structure.
- Blind SQL Injection: Extracts data without error messages, relying on the application’s response.
- Boolean-based SQLi: Determines success based on true/false outcomes.
- Time-based SQLi: Delays the application’s response to discern query success.
Prevention Strategies

Preventing SQL Injection requires a multi-faceted approach:
- Training and awareness: Educate all members of the team on SQL Injection risks.
- User input validation: Treat all input as untrusted and use whitelists instead of blacklists.
- Adopt latest technologies: Utilize modern development environments and technologies.
- Verified mechanisms: Employ built-in protection mechanisms like parameterized queries or stored procedures.
- Regular scanning: Use web vulnerability scanners to detect and mitigate vulnerabilities proactively.
Live demo example of SQL INJECTION Attack
For the live demo example i turned to the portswigger SQL INECTION labs. You can find the lab on this link https://portswigger.net/web-security/all-labs#sql-injection
Demo LAB 1
LAB 1 : https:/https://portswigger.net/web-security/sql-injection/lab-retrieve-hidden-data OR search it in all labs of port swaggers by the name of “Lab: SQL injection vulnerability in WHERE clause allowing retrieval of hidden data“
When you open this lab of portswigger you will notice that we have given a random webiste to attack with SQL Injection and also we have give some information that what the task we have to perform on that website.
Given Details:

End Goals:
To solve the lab, perform a SQL injection attack that causes the application to display one or more unreleased products.
Now access the lab and you will see this type of site showing all the products and categories.

Now we have to perform SOL Injection on this site to know the latest unreleased product.
From the given data we can see that we have to attack on gifts section page we will try using different types of query methods to solve this lab.
First we try using the most used query (” ” “) as you can see in screenshot

But when we are executing this query we are getting no result but also we are getting this information that this query has been executed successfully with no error but now we cant see the image of the product.

So now running some different queries with this query to see the result.

Hooray! After executing the query '+OR+1=1--, we’ve successfully cracked our first demo lab! Now, we can finally view the desired content on the website. This query worked like magic, granting us access to the site’s information.
Demo LAB 2
LAB 2: https://portswigger.net/web-security/sql-injection/lab-login-bypass OR search it in all labs of port swaggers by the name of ” Lab: SQL injection vulnerability allowing login bypass “.
When you open this lab of portswigger you will notice that we have given a random webiste to bypass the login field.
Given Task:

In this we have already given that we have to login in the application as an administrator.
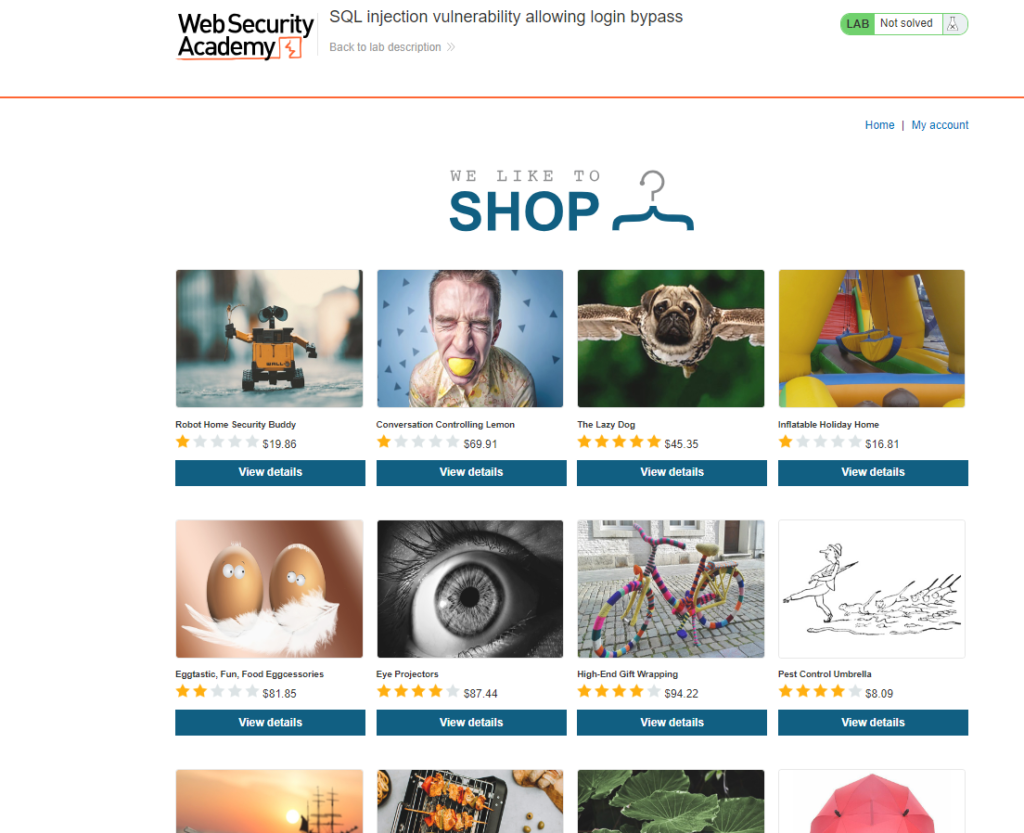
Now going to my account page and try to take administrator access.
Trying with the “”administrator’– “” username and password at random lets see the result.


Hooray! After executing the query administrator'-- in both the username and password fields at random, we’ve successfully cracked our first demo lab! Now, we can finally view the desired content on the website. This query worked like magic, granting us access to the site’s information.

